Mapping Windows Active Directory security groups to ClickHouse roles
Example
This example shows how AD users that belong to different AD security groups can be given role access in ClickHouse. It also shows how a user may be added to multiple AD user groups so they can have access provided by multiple roles.
In this environment, we have the following:
- A Windows Active Directory domain:
marsnet2.local - A ClickHouse Cluster,
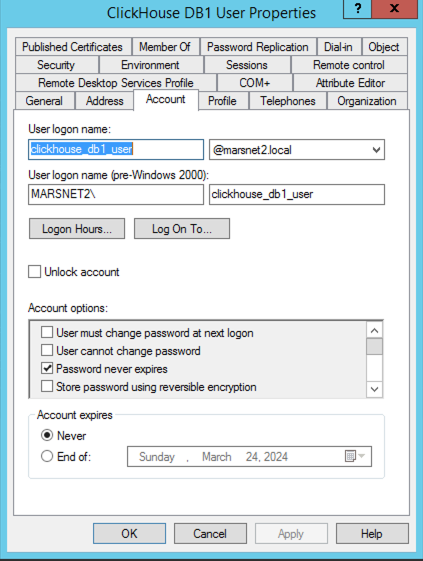
cluster_1S_3Rwith 3 nodes on a cluster configuration of 1 shard, 3 replicas - 3 AD users
| AD User | Description |
|---|---|
| clickhouse_ad_admin | ClickHouse Admin user |
| clickhouse_db1_user | User with access to db1.table1 |
| clickhouse_db2_user | User with access to db2.table1 |
| ch_db1_db2_user | User with access to both db1.table1 and db2.table1 |
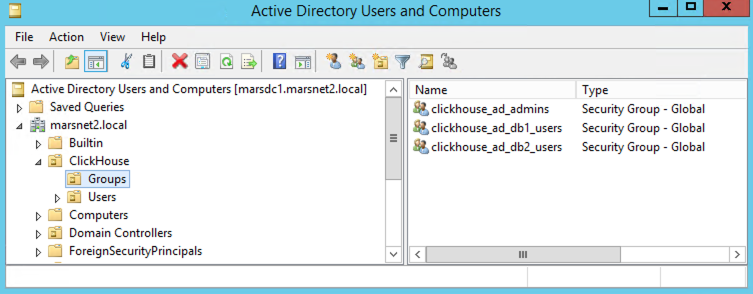
- 3 AD security groups
| AD Group | Description |
|---|---|
| clickhouse_ad_admins | ClickHouse Admins group |
| clickhouse_ad_db1_users | Group to map with access to db1.table1 |
| clickhouse_ad_db2_users | Group to map with access to db2.table1 |
- Example AD Environment and UO structure:
- Example AD Security Group Configuration:

- Example AD User Configuration:
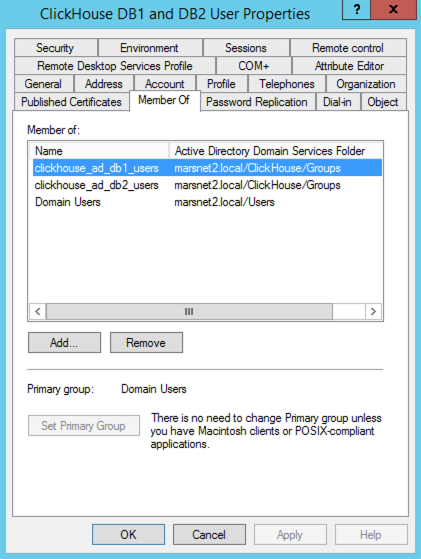
- In Windows AD Users and Groups, add each user to their respective group(s), they will be mapped to the ClickHouse roles (example in the next step).
| AD Security Group | ClickHouse Role |
|---|---|
| clickhouse_ad_admin | clickhouse_ad_admins |
| clickhouse_db1_user | clickhouse_ad_db1_users |
| clickhouse_db2_user | clickhouse_ad_db2_users |
| ch_db1_db2_user | clickhouse_ad_db1_users and clickhouse_ad_db2_users |
- Example user group membership:
- In ClickHouse
config.xml, add theldap_serversconfiguration to each ClickHouse node.
| xml tag | Description | Example Value |
|---|---|---|
| ldap_servers | Tag used to define the ldap servers that will be used by ClickHouse | NA |
| marsnet_ad | This tag is arbitrary and is just a label to use to identify the server in <user_directories> section | NA |
| host | FQDN or IP Address of Active Directory server or domain | marsdc1.marsnet2.local |
| port | Active Directory Port, usually 389 for non-ssl or 636 for SSL | 389 |
| bind_dn | Which user will be used to create the bind to AD, it can be a dedicated user if regular users are not allowed to | {user_name}@marsnet2.local |
| user_dn_detection | Settings on how ClickHouse will find the AD users | NA |
| base_dn | AD OU path to start the search for the users | OU=Users,OU=ClickHouse,DC=marsnet2,DC=local |
| search_filter | ldap search filter to find the AD user | (&(objectClass=user)(sAMAccountName={user_name})) |
Refer to documentation for full set of options: https://clickhouse.com/docs/en/operations/external-authenticators/ldap#ldap-server-definition
- In ClickHouse
config.xml, add the<user_directories>configuration with<ldap>entries to each ClickHouse node.
| xml tag | Description | Example Value |
|---|---|---|
| user_directories | Defines which authenticators will be used | NA |
| ldap | This contains the settings for the ldap servers, in this AD that will be used | NA |
| server | This is the tag that was define in the <ldap_servers> section | marsnet2_ad |
| role_mapping | definition on how the users authenticated will be mapped between AD groups and ClickHouse roles | NA |
| base_dn | AD path that the system will use to start search for AD groups | OU=Groups,OU=ClickHouse,DC=marsnet2,DC=local |
| search_filter | ldap search filter to find the AD groups | (&(objectClass=group)(member={user_dn})) |
| attribute | Which AD attribute field should be used to identify the user | CN |
| scope | Which levels in the base DN the system should search for the groups | subtree |
| prefix | Prefix for the names of the groups in AD, this prefix will be removed to find the roles in ClickHouse | clickhouse_ |
Refer to documentation for full set of options: https://clickhouse.com/docs/en/operations/external-authenticators/ldap#ldap-external-user-directory
note:::
Since the AD security groups were prefixed in the example - i.e. clickhouse_ad_db1_users- when the system retrieves them, the prefix will be removed and the system will look for a ClickHouse role called ad_db1_users to map to clickhouse_ad_db1_users.
:::
- Create example databases.
- Create example tables.
- Insert sample data.
- Create ClickHouse Roles.
- Grant the privileges to the roles.
- Test access for restricted db1 user. For example:
- Test access for the user that has access to both databases, db1 and db2. For example:
- Test access for the Admin user. For example: